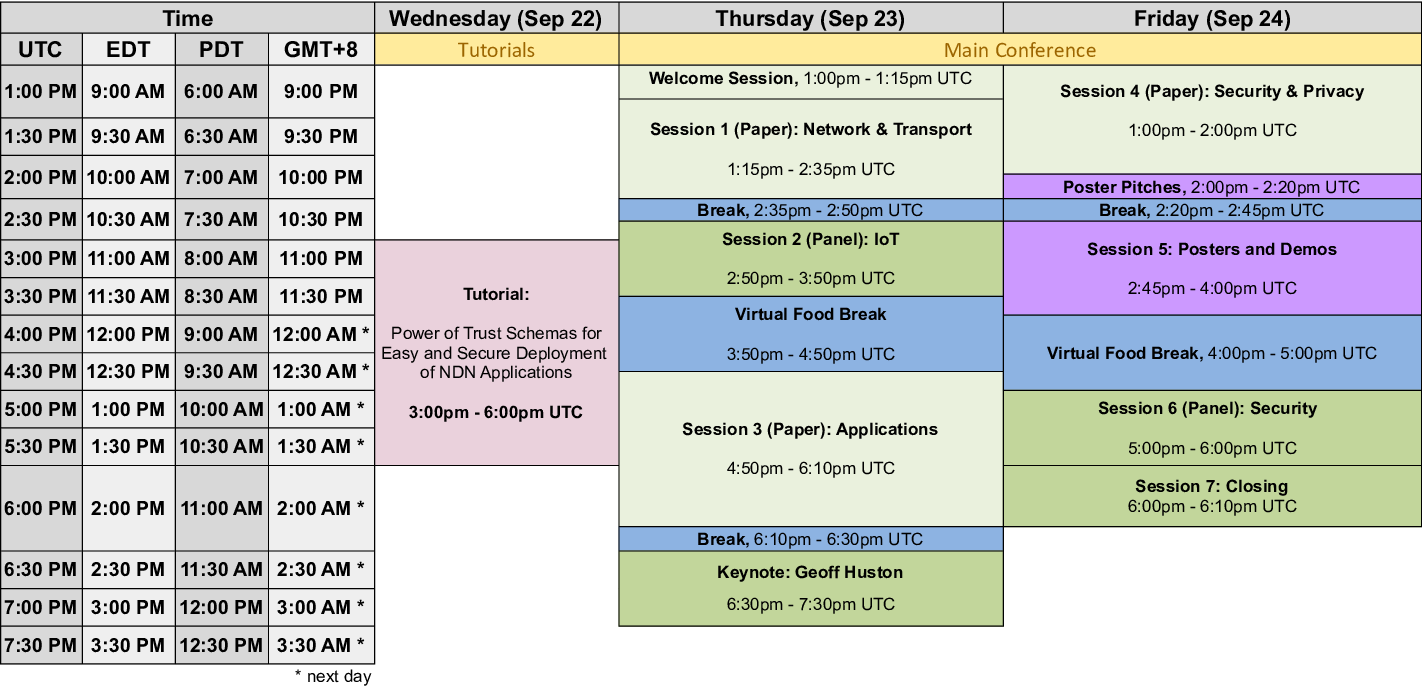
8th ACM Conference on Information-Centric Networking (ICN 2021), Sept. 22–24, 2021
Preliminary Conference Program
Kindly note that the schedule below is tentative and subject to updates.
Conference Schedule at a Glance
Schedule
- Tutorial day with afternoon tutorials in parallel
-
3pm - 6pm UTC Tutorial: Power of Trust Schemas for Easy and Secure Deployment of NDN Applications
- Welcome Session
- Session 1 (Paper): Network & Transport
-
NDN in Large LEO Satellite Constellations: A Case of Consumer Mobility Support
Teng Liang (Peng Cheng Laboratory), Zhongda Xia (Harbin Institute of Technology), Guoming Tang (Peng Cheng Laboratory), Yu Zhang (Harbin Institute of Technology), Beichuan Zhang (University of Arizona)
-
Abstract:
Large low Earth orbit (LEO) satellite constellations are intended to provide global low-latency high-bandwidth Internet connectivity. Due to their large scale and high mobility nature, networking is a big challenge. In this paper, we investigate applying Named Data Networking (NDN) to this scenario. Specifically, we discuss that NDN's architectural benefits, such as adaptive forwarding, in-network caching, off-the-grid communication, data mule service, in-network/edge computing, mobility support, and data-centric security, make it a promising candidate. Moreover, we focus on studying NDN's consumer mobility support. Specifically, NDN's in-network Interest retransmission can quickly react to satellite handovers. However, we make an observation that Interest routing paths before and after satellite handover may not overlap, hence underusing NDN's in-network caching. Therefore, we direct retransmitted Interests due to handovers to the previous connected satellite via forwarding hint. Simulation results show that the studied approaches can decently improve the consumers' performance and reduce the network traffic, achieving better consumer mobility support.
-
-
Vision: Toward 10 Tbps NDN Forwarding with Billion Prefixes by Programmable Switches
Junji Takemasa (Osaka Univeristy), Yuki Koizumi (Osaka University), Toru Hasegawa (Osaka University)
-
Abstract:
This paper designs a Named Data Networking (NDN) router architecture that leverages switching speed of a programmable switch and a large capacity of DRAM devices of commodity servers. The key idea is that Data packets are forwarded by a switch ASIC alone, whereas Interest packets are forwarded by an NDN forwarding engine at a server. This paper validates that the architecture is able to achieve the 10-Tbps throughput of Data packets by analyzing bottlenecks for high-speed forwarding. The prototype implementation with a Tofino switch and a commodity server demonstrates about 470 Gbps throughput when using a single pipeline of its switch ASIC.
-
-
LPECN: Leveraging PIT placement and Explicit marking for Congestion control in NDN
Madhurima Buragohain (Indian Institute of Technology Guwahati), Sukumar Nandi (Indian Institute of Technology Guwahati)
-
Abstract:
Named Data Networking (NDN) is designed to address several limitations of the current Internet, such as inefficient content delivery, mobility and security. Pending Interest Table (PIT) is one of the fundamental building blocks in NDN. Its unique design contributes various advantages such as stateful forwarding plane, loop detection, similar request aggregation, multipath forwarding and multicast. However, PIT size may become a bottleneck in network performance in the presence of bursty traffic or unresponsive consumers. Therefore, we propose a congestion control scheme that leverages PIT placement and explicit congestion marking. We have used PIT per outgoing face placement to efficiently limit the Interest sending rate according to the available capacity of the link, which can avoid congestion in the reverse path. In addition that, we utilize Negative Acknowledgement and explicit congestion marking to efficiently detect and limit interests from non-responsive consumers. From the simulation result, we have shown that our proposed scheme can efficiently handle congestion even in the presence of non-responsive consumers.
-
-
YaNFD: Yet another Named Data Networking Forwarding Daemon
Eric Newberry (UCLA), Xinyu Ma (UCLA), Lixia Zhang (UCLA)
-
Abstract:
We have developed YaNFD as a new software packet forwarder for NDN. YaNFD achieves compatibility with existing NDN applications and forwarders, as well as high throughput. YaNFD features multi-threaded forwarding, a smaller and more streamlined codebase compared to existing implementations, and can be managed using existing NDN forwarder management utilities and protocols. In this paper, we discuss our implementation, including how it differs from previous forwarders based upon lessons learned during their development and use over the span of multiple years. Additionally, we present the lessons learned from our experience developing a new forwarder for NDN from the ground up.
-
- Break
- Session 2 (Panel)
-
Panel: Are we ready to build a data-centric Internet of Things?
Abstract: Since the early days of wireless sensor networks, the search for optimized ways of accessing data in the constrained wireless world continues. Name-based routing with content object security and hop-wise forwarding with in-network caching have been repeatedly considered to form a data-centric Internet of Things. With OSCORE and CoAP Proxy, the IETF currently standardises building blocks that support this vision. Is the community ready to converge on these information-centric principles for the IoT?
Panelists:
Jari Arkko (Ericsson)
Christian Amsüss (n/a)
Nikos Fotiou (Athens University of Economics and Business)
Dirk Kutscher (University of Applied Sciences Emden/Leer) - Virtual Food Break
- Session 3 (Paper): Applications
-
High Performance Adaptive Video Streaming using NDN WLAN Multicast
Wang Yang (Central South University, China), Fan Wu (Tsinghua University, China), Kaijin Tian (Central South University, China)
-
Abstract:
Multicast is a promising technology for rapidly-increasing video streaming in Wireless Local Area Networks (WLAN). NDN's implicit multicast and caching capabilities provide strong benefits in multicast transmission and can significantly improve network transmission efficiency. However, existing WLAN multicast schemes use the basic data rate to transmit the multicast data. The basic data rate cannot support high-quality video transmission, which significantly reduces the user's Quality of Experience (QoE). In addition, the NDN architecture follows the One-Interest-One-Data transmission principle, so that the uplink will have to face fierce competition, especially when the number of stations has increased significantly. In this paper, we propose HPNM, a High Performance adaptive video streaming scheme by using NDN WLAN Multicast. To improve the Interest sending efficiency in the NDN Live video scenario, we propose an AP(Access Point)-based Interest proxy mechanism that mitigates WLAN channel competition as the number of Interest sending packets increases. In addition, we propose a layer-based NDN WLAN multicast data rate selection mechanism for the adaptive Scalable Video Coding (SVC) video streaming, which can further improve the video bitrate. We use ndnSIM to evaluate the performance of HPNM in terms of video bitrate, startup time, and stalling time. The evaluation results show that the average video bitrate of HPNM has increased significantly compared with the existing scheme in the background traffic scenario.
-
-
Vision: Information-Centric Dataflow – Re-Imagining Reactive Distributed Computing
Dirk Kutscher (University of Applied Sciences Emden), Laura Al Wardani (University of Applied Sciences Emden), T M Rayhan Gias (University of Applied Sciences Emden)
-
Abstract:
This paper describes an Information-Centric Dataflow system that is based on name-based access to computation results, NDN PSync dataset synchronization for enabling consuming compute functions to learn about updates and for coordinating the set of compute functions in a distributed Dataflow pipeline. We describe how relevant Dataflow concepts can be mapped to ICN and how data-sharing, data availability and scalability can be improved compared to state-of-the-art systems. We also provide a specification of an application-independent namespace design and report on our experience with a first prototype implementation.
-
-
Reliable Firmware Updates for the Information-Centric Internet of Things
Cenk Gündoğan (HAW Hamburg), Christian Amsüss, Thomas C. Schmidt (HAW Hamburg), Matthias Wählisch (FU Berlin)
-
Abstract:
Security in the Internet of Things (IoT) requires ways to regularly update firmware in the field. These demands ever increase with new, agile concepts such as security as code and should be considered a regular operation. Hosting massive firmware roll-outs present a crucial challenge for the constrained wireless environment. In this paper, we explore how information-centric networking can ease reliable firmware updates. We start from the recent standards developed by the IETF SUIT working group and contribute a system that allows for a timely discovery of new firmware versions by using cryptographically protected manifest files. Our design enables a cascading firmware roll-out from a gateway towards leaf nodes in a low-power multi-hop network. While a chunking mechanism prepares firmware images for typically low-sized maximum transmission units (MTUs), an early Denial-of-Service (DoS) detection prevents the distribution of tampered or malformed chunks. In experimental evaluations on a real-world IoT testbed, we demonstrate feasible strategies with adaptive bandwidth consumption and a high resilience to connectivity loss when replicating firmware images into the IoT edge.
-
-
FLARE: Federated Active Learning Assisted by Naming for Responding to Emergencies
Viyom Mittal (University of California, Riverside), Mohammad Jahanian (University of California, Riverside), K. K. Ramakrishnan (University of California, Riverside)
-
Abstract:
During disasters, it is critical to deliver emergency information to appropriate first responders. Name-based information delivery provides efficient, timely dissemination of relevant content to first responder teams assigned to different incident response roles. People increasingly depend on social media for communicating vital information, using free-form text. Thus, a method that delivers these social media posts to the right first responders can significantly improve outcomes. In this paper, we propose FLARE, a framework using 'Social Media Engines' (SMEs) to map social media posts (SMPs), such as tweets, to the right names. SMEs perform natural language processing-based classification and exploit several machine learning capabilities, in an online real-time manner. To reduce the manual labeling effort required for learning during the disaster, we leverage active learning, complemented by dispatchers with specific domain-knowledge performing limited labeling. We also leverage federated learning across various public-safety departments with specialized knowledge to handle notifications related to their roles in a cooperative manner. We implement three different classifiers: for incident relevance, organization, and fine-grained role prediction. Each class is associated with a specific subset of the namespace graph. The novelty of our system is the integration of the namespace with federated active learning and inference procedures to identify and deliver vital SMPs to the right first responders in a distributed multi-organization environment, in real-time. Our experiments using real-world data, including tweets generated by citizens during the wildfires in California in 2018, show our approach outperforming both a simple keyword-based classification and several existing NLP-based classification techniques.
-
- Break
- Keynote
-
Keynote: Today’s Internet Question: Is “Big" necessarily "Bad?”
Geoff Huston (APNIC)
Abstract: The topic of "Internet Centrality" has gained much in the way of prominence in recent years as a small number providers dominate various aspects of the digital environment. In this presentation I would like to add a little in the way of historical perspective to this conversation by looking at the economic thinking that lead to anti-trust legislation in the United States over a century ago and its application into today’s world. Do these digital giants pose a distortional threat to markets for good and services in this digital space simply by virtue of their size? Or should we judge their impact by their actions alone? I’d like to explore the thinking behind these positions and look at how it applies to day’s world.
 Bio: Geoff Huston AM is the Chief Scientist at APNIC. He is a mathematician by formal education, an Internet Engineer turned researcher by
profession and an amateur economic historian by inclination. He has worked in the academic sector building a national ISP in the early
days of the Internet, worked in the telco sector to construct a national consumer Internet service, and then worked in the naming,
addressing and routing infrastructure of the Internet as a researcher. His current interests include routing security, the domain name
system and transport protocol performance. He has been involved in the IETF for most of his career, and has chaired a number of Working
Groups as well as being on the Internet Architecture Board. He has authored three technical books and numerous RFCs.
Bio: Geoff Huston AM is the Chief Scientist at APNIC. He is a mathematician by formal education, an Internet Engineer turned researcher by
profession and an amateur economic historian by inclination. He has worked in the academic sector building a national ISP in the early
days of the Internet, worked in the telco sector to construct a national consumer Internet service, and then worked in the naming,
addressing and routing infrastructure of the Internet as a researcher. His current interests include routing security, the domain name
system and transport protocol performance. He has been involved in the IETF for most of his career, and has chaired a number of Working
Groups as well as being on the Internet Architecture Board. He has authored three technical books and numerous RFCs.
- Session 4 (Paper): Security & Privacy
-
NDN-MPS: Supporting Multiparty Authentication over Named Data Networking
Zhiyi Zhang (UCLA), Siqi Liu (UCLA), Randy King (Operant Networks), Lixia Zhang (UCLA)
-
Abstract:
Modern digitally controlled systems require multiparty authentication to meet the security requirements. This paper describes the design and development of NDN-MPS, an automated solution to support multiparty signing and verification for NDN-enabled applications. NDN-MPS proposes three basic changes to the existing NDN security solutions. First, it introduces a new type of trust schema that supports the semantics for multiparty singing and verification. Second, it extends the NDN signing process design to accommodate multisignature schemes such as BLS signature and to ensure the data consistency across signers. Third, NDN-MPS provides options for different application scenarios to coordinate the joint signing process of multiple signers. We evaluate NDN-MPS by assessing its security properties and measuring its performance. Our results show that NDN-MPS provides resistance against different types of attacks and is practical to be deployed.
-
-
Trust Schemas and ICN: Key to Secure Home IoT
Kathleen Nichols (Pollere, Inc.)
-
Abstract:
Home and business internet of things (IoT) networking presents security challenges that can be addressed using information-centric networking (ICN) to secure information rather than channels. In particular, we leverage ICN's per-packet signing, combined with recent innovations in trust schemas, to construct a strong trust zone. This architecture creates domains governed by a secured trust schema provided to every device during its enrollment together with the device's attribute-based signing cert chain(s). Applications don't need to be rewritten to gain security; a run-time library with an MQTT-like publish/subscribe API uses the provisioned trust schema and certs to construct, sign and ship outgoing publications and to both cryptographically and structurally validate a subscriber's incoming publications. This unique application of trust schemas (Versec) is explained and an example home IoT framework is described where trust schemas express straightforward, homeowner-specific policies that an open-source library enforces at run-time on behalf of security-agnostic applications. Along with the specific innovation in trust management, the platform exploits current and emergent IoT best practices. Utility programs, libraries, and examples are available as an open-source Data-Centric Toolkit.
-
-
Analyzing GDPR Compliance of Named Data Networking
Casey Tran (New Mexico State University), Reza Tourani (Saint Louis University), Satyajayant Misra (New Mexico State University), Travis Machacek (New Mexico State University), Gaurav Panwar (New Mexico State University)
-
Abstract:
The popularity of social media platforms, Internet of Things (IoT) devices, and the myriad smartphone applications have created opportunities for companies and organizations to collect individuals' personal data and monetize its sharing at a high rate. A standout example was the Facebook--Cambridge Analytica data-sharing arrangement (2018), which allowed Cambridge Analytica to harvest millions of Facebook users' personal data without their consent for political advertisement. In response to such overreach and privacy violations, the European Union introduced the General Data Protection Regulation (GDPR), which mandates data collectors to protect individuals' data privacy and provide the user more control over their personal data. Motivated by this growing interest in personal privacy, we analyze GDPR articles in the context of Named Data Networking (NDN). The context of interest is NDN as the network architecture in a service provider and we investigate GDPR-pertinent NDN features, including naming, caching, forwarding plane, and its built-in trust, for GDPR compliance and present insights on how such compliance can be built, when lacking. We also present experimental results showing compliance overheads and conclude by identifying potential future work.
-
- Poster Pitches
- Break
- Session 5: Posters and Demos
-
Attribute-Based Encryption for Named Data Networking
Aleksandr Lenin and Peeter Laud (Cybernetica AS)
-
Abstract:
We compare and discuss the applicability and trade-offs of different attribute-based encryption (ABE) schemes to the possible use-cases of content-centric networking requiring end-to-end encryption of data with fine-grained access control, where the nature of content producers and consumers may vary, as well as the required expressivity of policies. We also report on the choice and implementation of an ABE scheme, as well as the overheads associated with its use.
-
-
GitSync: Distributed Version Control System on NDN
Xinyu Ma and Lixia Zhang (UCLA)
-
Abstract:
Git is designed as a distributed version control system which has been widely used. However, most of the existing projects use a workflow where developers have to synchronize with a central server. This poster explores the possibility of a truly distributed git platform, dubbed GitSync, by making git run over Named-data Networking (NDN). GitSync runs a peer-to-peer protocol to get rid of central servers, therefore enabling higher availability when not all users are connected to cloud all the time. Therefore GitSync eliminates single point of failure and can continue operation over unstable connectivity and network partition.
-
-
ccnGen: A High-speed Generator of Bidirectional CCN Traffic Using A Programmable Switch
Junji Takemasa, Ryoma Yamada, Yuki Koizumi, and Toru Hasegawa (Osaka University)
-
Abstract:
This paper designs ccnGen, which generates request-response bidirectional CCN traffic, using a programmable switch. A prototype implementation demonstrates that one pipeline of the switch ASIC generates Interest packets of 232 64-byte names randomly with a uniform distribution and another one replies to the Interest packets by sending Content Object packets with the requested names at 1.6 Tbps speed.
-
-
In-vehicle Networking with NDN
Christos Papadopoulos (University of Memphis), Susmit Shannigrahi (Tennessee Technological University), and Alex Afanasyev (Florida International University)
-
Abstract:
In-vehicle networks have been relying on primitive technologies that provide neither security nor high-throughput. As in-vehicle communication becomes more sophisticated, the automotive community is looking for better security and performance. In this work we argue for NDN as a solution for the future of the automotive community.
-
-
Mnemosyne: An Immutable Distributed Logging Framework over Named Data Networking
Siqi Liu, Philipp Moll, and Lixia Zhang (UCLA, Computer Science)
-
Abstract:
This poster describes the design of Mnemosyne, a distributed logger running over Named Data Networking. Mnemosyne utilizes proof of authenticity instead of proof of work. It assures immutability of logged events by interlocking all event records in a DAG mesh. By using a distributed design, Mnemosyne provides both a high logging throughput and system resiliency in face of network component failures.
-
-
Supporting Pub/Sub over NDN Sync
Varun Patil, Philipp Moll, and Lixia Zhang (UCLA, Computer Science)
-
Abstract:
Distributed dataset synchronization, or Sync, plays the role of a transport layer protocol in Named Data Networking (NDN). The role of Sync is to synchronize the namespace of all data productions by multiple entities running the same application. NDN application developers desire a high level API, such as the commonly used pub/sub API that hides transport and network layer details. This poster explores the design of such an API built on top of State Vector Sync (SVS), one of the NDN Sync protocols, along with a low-latency data fetching option. With this API, SVS provides fast and resilient dataset synchronization, enabling developers to work with a familiar pub/sub API while benefiting from NDN’s capabilities of built-in data security, multicast data delivery, in-network caching, and consumer driven flow control.
-
-
DEMO: Decentralized ICN-based Dataflow System Implementation
Laura Al Wardani, T M Rayhan Gias, and Dirk Kutscher (University of Applied Sciences Emden/Leer)
-
Abstract:
This demo implements a distributed, data-oriented stream processing system. This system implements stream processing using Named Data Networking (NDN) -based communications. It exploits NDN-networking features to promote stream processing in an efficient, decentralized system.
-
-
Christopher Scherb (University of Basel), Dennis Grewe (Robert Bosch GmbH), and Christian Tschudin (University of Basel)
-
Abstract:
Today’s Internet is heavily used for multimedia streaming from cloud backends, while the Internet of Things (IoT) reverses the traditional data flow, with high data volumes produced at the network edge. Information Centric Networking (ICN) advocates against a host-centric communication model which is promising for distributed edge computing environments and the execution of IoT applications in a decentralized fashion. However, the tight coupling challenges network performance due to additional synchronization overhead of large data volumes and services. We present Tangle Centric Networking (TCN) – a decentralized data structure for coordinated distributed applications and data exchange following principles of ICN. TCN can react on data and service changes and update them accordingly in network nodes, provide distributed data structures and enable cooperative work on the same data without huge overhead by using Tangles for coordination. We implemented TCN in simulations and evaluated the concept against a base line scenario.
-
-
Exploring Rate-Based Congestion Control in NDN
Sichen Song and Lixia Zhang (University of California, Los Angeles)
-
Abstract:
We report our work-in-progress in designing a rate-based congestion control for NDN networks. We first explain why rate-based approach represents a more promising direction compared to the existing window-based congestion control solutions, and then provide a sketch of our initial design, together with a few lessons we have learned and some preliminary results in pursuing this new direction.
-
- Virtual Food Break
- Session 6 (Panel)
-
Panel: Can ICN architectures solve hard problems in network security
Abstract: ICN protocols are often said to be more secure than IP. Can use of ICN protocols make networked security better and easier to implement? Is there work in the security field that should be added to ICN protocols and architectures? What should the community be working on that could lead to a world without news stories of major security breaches?
Panelists:
Eric Osterweil (George Mason University)
Ned Smith (Intel Corp)
Dan Massey (US Dept of Defense)
Christos Papadopoulos (University of Memphis)
Jan Seedorf (Hochschule fur Technik Stuttgart) - Session 7: Closing
-
Announcement of ACM ICN 2022